Using SMB it is possible to retrieve data that is typically only expected when carrying out host based forensics. The MACB (Modification, Access, Change and Birth) data is sent across regardless of if a file is accessed or not.
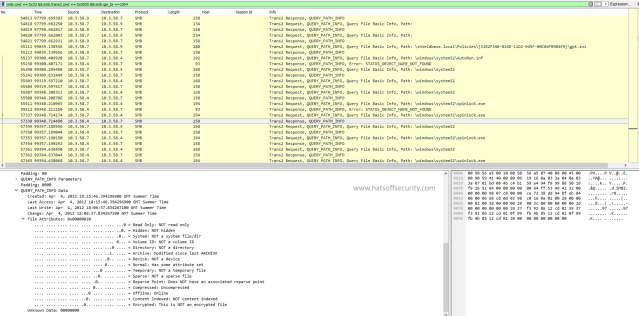
With SMB v1 this was a bit of a pain to find, the Wireshark filter required was
smb.cmd == 0x32 && smb.trans2.cmd == 0x0005 && smb.qpi_loi == 1004
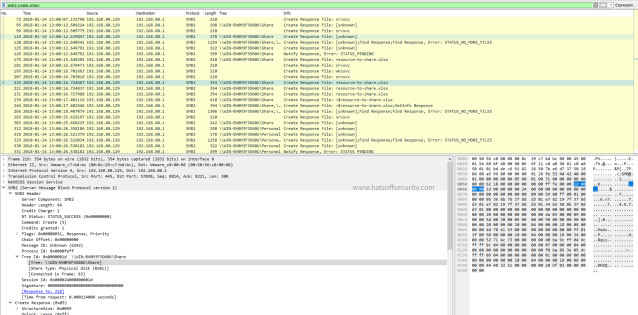
with SMBv2 it is simper
smb2.create.action
This command can have a value added after it, however in its current state it is the equivalent of having “exists” on the end.
The output looks different to SMBv1 as you would expect, but the data is the same.
SMBv1
SMBv2
With SMBv2, the simple addition of a column provides us with the path detail that was removed from the SMBv1 command
Why do I care?
As you can see from the screenshots, this shows what files were accessed. If you look closely at the second screenshot you can see that a file named “~$resource-to-share.xlsx” was referenced. When you look at this you can see it talks about a file being created on the share. This tells us two things.
- We can see when files are uploaded to an SMB share
- The Excel file was opened on the local machine as that is the temporary file Office creates to allow auto recovery on crash
The above is from a Windows Server 2016 VM I have in my home lab, but I have also tested this on my NAS and got the same type of results.

Pingback: Week 3 – 2018 – This Week In 4n6