When carrying out investigations there may be a whole raft of information that you have been given, from memory captures, logical or physical disk captures, or, you my have virtually nothing. As such I like to look at a variety of ways of gathering the same information. User accounts can be a tricky one, as the /users/<username> directory will only be created if that account has logged on to that machine (interactively/RDP etc) so in my mind not a reliable way to determine what user accounts existed on that box.
The SAM database however, is where the user account information is stored. So in this case should be a good first port of call for this information.
There are two good options (actually there are many, but I am going to show you two) for SAM data extraction. I will be showing you:
and
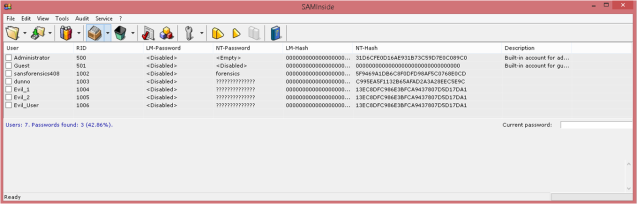
SAMInside needs two hives: SAM & System to carry out it search, it will also attempt to crack the passwords of the accounts (I wont be covering the password cracking feature in this post). After you have pointed SAMInside at your offline Hives you will be presented with the following screen:
This tool shows you the LM-Hash or NT-Hash that is in use. The Administrator account has no password (by default in Windows 8) as such the NT-Hash which is displayed would be the same for any account without a password; the ‘NT-Password’ field additionally tells us the password is ‘<empty>’. SAMInside also gives us the RID (Relative Identifier) for the account, this will be important for later forensic work, I suggest making a note of it for any suspect accounts.
The second of our tools is regripper. regripper is not solely designed for the SAM database, it is more like a Windows auto-grep tool which has pre-loaded modules. It basically takes a lot of the hard work out of grep’ing these files manually!
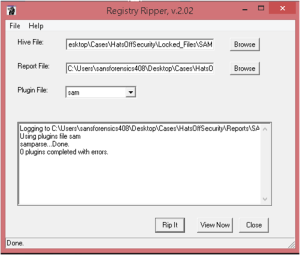
When running regripper it will ask you for the location of the Hive, the location of the output report and which module you wish to run.
Once you hit ‘Rip It’ you will see the above screen, from here you can either ‘view now’ or go to your report manually. Two files are created; a log file and the report. The log file is useful if there are errors.
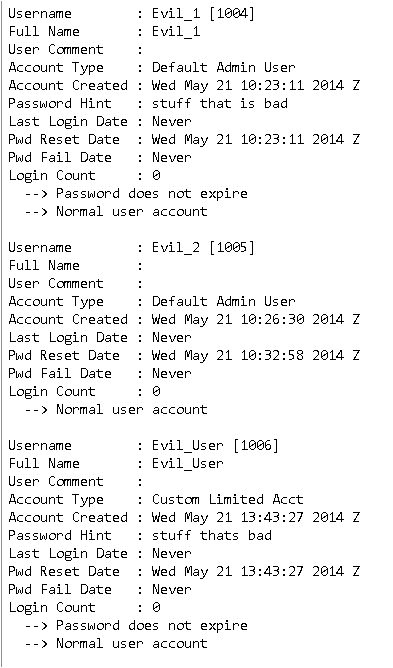
This is part of the report you will be shown, there is also information on group memberships. The reason I am showing this screenshot is not because of the evil nature of the account names, but ‘Evil_2’ is different to the other two Evil accounts. For example the Full name is missing, there is no password hint (which Windows 8 forces you to put in) and the password fail date is set to ‘never’ although the account does not specify this in the text below.
The reason for this is because Evil_2 was created using a command prompt not the Windows user GUI, this is obviously very important due to the nature of many attacks taking place on the command line. Noticing (and documenting) these differences can help identify rogue user accounts when your attacker is slightly more subtle than this one.
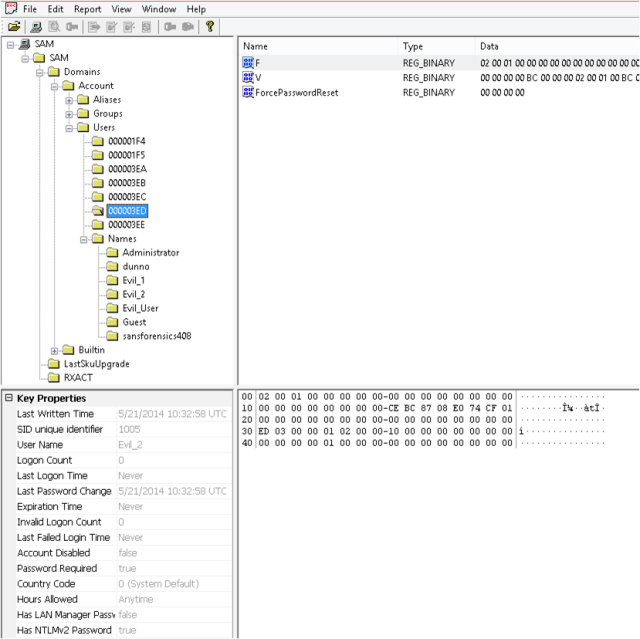
Very quickly I also want to show you how the above tools are far easier than attempting to do this manually using only Registry Viewer.
Simply open the SAM Hive file in Registry Viewer and browse to SAM\Domains\Account\Users this will display the following:
Registry Viewer will parse some of the information, however an important note here is that ‘Has NTLMv2 Password’ seen at the bottom left of the screenshot is not indicative of a password being set. I tested this with another account with no password and the same field was still set as ‘True’. Although this tool is not as pretty as the above two tools, it does offer you the chance to view the raw data to confirm your tools are working as expected.

Hello Mr. Taylor
I am trying to find out when certain user accounts were both created and deleted on a system running XP. I know that a user account has been made, then deleted and then another made again with the same username. Will either of these methods help me in finding out when the original accounts were created? It was back in 2008, so I’m not sure if it is retained for that long.
I haven’t had chance to do any testing on this yet, however the SID of the user accounts are unique, if the account was deleted and a new account created it would have a new SID (regardless of username). If the SAM database can help, it will be a case of figuring out; if when an account is deleted does the SAM delete the corresponding keys? If it does this becomes a bit more challenging, if it doesn’t you should be able to get some dates from the keys themselves (created and last write time are your best bets).
You may also be able to look elsewhere on the machine for information. The Journal file contains a timeline of when each file/folder was created. However I am not sure how far back that goes. If it does keep everything, you could determine the first time that user logged on by the creation time of the user profile and the time the replacement user logged on by the creation of a new User profile with a similar name (I think XP addded _001 for duplicate user account names, but I might be wrong).
If the user profile still exists you can get data from there too, the NTUser.dat would contain dates regarding first/last logon with created and last modified dates.
I hope all of this helps, I will try and have a look tonight (CET) to see if I can replicate this and get you a better answer.
Cheers, Russ.